Phishing has changed over time.
It’s no longer awkward emails with misspellings and dubious links in 2026. Phishing tactics nowadays are smart, automated, tailored, and frequently driven by AI algorithms that can respond more quickly than human security teams.
We witness this change on a daily basis at One Ten Technologies. You’re using human speed tools to combat a machine speed threat if your company still uses manual review procedures and conventional email filters.
Let’s examine what phishing looks like in 2026 and how it is instantly eliminated by contemporary, AI-powered, self-governing defense.
Explain a Phishing Attack and Why It Is More Dangerous Than Before.
Phishing is a kind of cyber attack in which a person acts as a trustworthy source in order to trick you into:
- Revealing login credentials
- Accepting fake payments
- Getting malicious software
Revealing personal information
The trick, however, is this:
Computer systems are not compromised by phishing attacks. People get phished. Instead of exploiting vulnerabilities, attackers use authority, rush, fear, and trust.
What Modern Phishing Looks Like in 2026
Modern phishing attacks are:
- AI-created and grammatically correct
- Personalized using data scraped from public sources
- Multi-modal (email, SMS, voice, chat messaging)
- Adaptive and learning
- Designed to evade traditional security filters
Spelling mistakes? History.
Generic salutations? A rarity.
Mass mailings? Now replaced by targeted attacks.
| Category | 2020 Phishing | 2026 Phishing |
| Language Quality | Poor grammar | AI-perfect writing |
| Targeting | Broad & generic | Hyper-personalized |
| Channels | Mostly email | Email + SMS + Voice + Chat |
| Speed | Human-operated | Machine-speed automation |
| Detection Evasion | Static templates | Polymorphic & adaptive |
| Success Rate | Moderate | Significantly higher |
The Modern Phishing Lifecycle (Step-by-Step)
Here’s how advanced phishing campaigns typically unfold:
| Stage | What Happens | Why It’s Effective |
| Reconnaissance | Attackers gather employee data from social media & breaches | Personalization increases trust |
| Domain Setup | Lookalike domains are registered | Bypasses reputation filters |
| Psychological Trigger | Urgency, authority, or reward messaging | Overrides rational judgment |
| Credential Harvesting | Victim enters credentials into fake site | Immediate access gained |
| Lateral Movement | Attackers pivot internally | Expands damage rapidly |
One compromised credential can lead to:
- Ransomware
- Business email compromise (BEC)
- Financial fraud
- Data exfiltration
- Regulatory fines
2026 Phishing Trends You Can’t Ignore
1. AI-Generated Phishing on a Large Scale
AI models are now capable of generating:
- Contextual emails
- Executive-sounding language
- Multilingual attacks
- Highly personalized emails
These emails are impossible to distinguish from real emails.
2. Voice & Deepfake Attacks
Thieves can now record the voice of an executive to sign off on fraudulent wire transfers.
Your finance department thinks they are talking to the real executive – when they are not.
3. Autonomous (Agentic) AI Attacks
AI systems can now:
- Plan an attack
- Test detection systems
- Automatically change the content
- Change domains instantly
- Optimize messages in real time
This is no longer “send and wait.”
It’s autonomous cyber attacks at machine speed.
4. Multi-Channel Reinforcement
A typical attack in 2026 might go like this:
- Email asking for a password reset
- SMS reminder to reinforce the urgency
- Voice call “confirming” the request
This multi-channel attack approach is much more successful.
Types of Phishing Attacks in 2026
| Attack Type | Description | Risk Level |
| Bulk Phishing | High-volume generic campaigns | Medium |
| Spear Phishing | Highly targeted individuals | High |
| Whaling | Executive-level targeting | Critical |
| Business Email Compromise | Impersonated payment requests | Critical |
| AI Phishing | Generative AI personalization | Severe |
| Vishing | Voice-based deception | High |
| Smishing | SMS-based phishing | Medium |
| Quishing | Malicious QR codes | Rising |
| Man-in-the-Middle | Intercepted communications | Severe |
Why Traditional Security Is Failing
Legacy solutions are based on:
- Static blacklists
- Domain signatures
- Previously known threats
Modern phishing attacks involve:
- Newly registered domains
- Dynamic content generation
- Contextual personalization
- Fast domain flipping
Static security solutions are simply not agile enough to handle adaptive AI attacks.
How One Ten Technology Neutralizes Phishing in Real Time
At One Ten Technology, we don’t just protect against phishing attacks.
We predict them.
Here’s how our cutting edge autonomous security solution works:
-
AI-Powered Behavioral Analysis
Rather than scanning for known malicious domains, we examine:
- User behavior patterns
- Tone changes in communication
- Unusual login attempts
- Device and session anomalies
- Credential entry into unauthorized domains
We analyze intent, not just indicators.
-
Phishing-Resistant Authentication
Traditional SMS authentication is no longer sufficient.
Modern security requires:
- Origin-bound authentication
- Hardware-secured verification
- Cryptographic verification
This protects against credential replay attacks and session hijacking.
-
Autonomous Containment
When a phishing attack is identified, automated processes can:
- Immediately revoke credentials
- Isolate compromised devices
- Block malicious domains
- Quarantine suspicious emails
- Notify security teams
All within minutes, not hours.
-
Predictive Digital Risk Protection
Rather than reacting to attacks that have already reached inboxes, we:
- Monitor for brand impersonation
- Detect lookalike domain registrations
- Identify spoofed accounts
- Search underground markets for leaked credentials
- Initiate rapid take down actions
The goal? Reduce dwell time to near zero.
Reactive vs Predictive Security
Here’s the difference:
| Legacy Security | AI-Enhanced Defense |
| Detects known threats | Detects unknown & emerging threats |
| Relies on signatures | Uses behavioral AI models |
| Human ticket escalation | Automated containment |
| Slow take down | Real-time response |
| Alert-based | Autonomous response |
The shift is clear.
Security must move from alerting humans to empowering autonomous systems.
Attack Speed vs Human Response
AI Attack Speed ████████████████████████████ (Seconds)
Human Detection Speed ████ (Hours)
Manual Response Speed ██ (Days)
Autonomous Response ██████████████████████ (Minutes)
You cannot close a seconds-wide attack window with days-long response workflows.
The Business Impact of AI-Driven Phishing
Let’s look at the reality:
| Metric | Impact |
| AI-generated phishing volume | Rapidly increasing |
| Credential compromise speed | Seconds |
| Lateral movement window | Minutes |
| Average breach cost | Multi-million dollar impact |
| Reputation damage | Long-term |
The financial and operational consequences are too large to ignore.
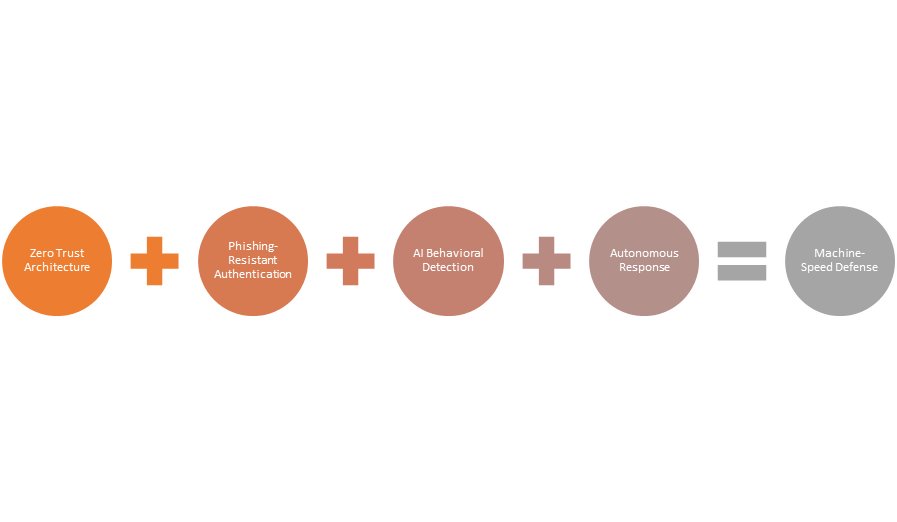
The One Ten Technology Way: Autonomy with Control
We envision the future of cybersecurity as:
- AI fighting AI
- Human intelligence directing automation
- Predictive protection prior to compromise
- Zero Trust architecture enforcement
- Continuous user risk scoring
Not more alerts.
Not more dashboards.
But smart, autonomous protection that eliminates threats before they materialize.
Business Leaders’ Action Plan in 2026
To lower phishing threats in 2023:
- Phishing will come to your organization. Assume it.
- Upgrade from signature-based solutions to AI-powered behavioral protection.
- Deploy phishing-resistant authentication.
- Automate incident response processes.
- Continuously monitor brand and domain impersonation.
- Regularly conduct phishing simulation attacks.
- Apply Zero Trust architecture to identity and access.
Phishing Risk Reduction Framework
Final Thoughts
Phishing in 2026 is not a nuisance.
It is an AI-driven, autonomous threat ecosystem capable of operating at machine scale.
But here’s the good news:
The same AI revolution empowering attackers is empowering defenders.
At One Ten Technology, we help organizations:
- Predict attacks
- Detect anomalies in real time
- Automatically contain threats
- Eliminate dwell time
- Build resilience against AI-driven cybercrime
You cannot fight machine-speed threats with manual processes.
But with the right autonomous defense strategy, you can stay ahead and keep your organization secure in the age of AI-powered phishing.


